In today’s rapidly evolving cyber threat landscape, protecting your digital assets is paramount. BreachLock is here to offer you comprehensive and reliable penetration testing services that will assess the security of your applications, networks, and cloud environments. Our unique human-delivered approach, combined with AI-powered technology, ensures accurate vulnerability identification, enabling you to safeguard your organization from potential cyberattacks. With a range of specialized pentesting services such as applications, API, network, cloud, DevOps, and IoT, BreachLock has the expertise to address your specific security needs. Benefit from our standardized framework, AI-powered technology, scalability, contextual insights, and industry compliance solutions. Choose BreachLock and take proactive steps to strengthen your organization’s security defenses. Get in touch with us today and start protecting your valuable digital assets.

Why Consider This Product?
When it comes to protecting your digital assets, you can’t afford to take any chances. That’s why BreachLock’s Human-Delivered Penetration Testing Services are the ideal solution for enhancing the security of your applications, networks, and cloud environments. With a combination of human expertise and advanced AI-powered technology, BreachLock ensures accurate vulnerability identification and helps you stay one step ahead of potential cyberattacks.
With an extensive range of services, including applications pentesting, API pentesting, network pentesting, cloud pentesting, DevOps pentesting, and IoT pentesting, BreachLock covers all aspects of cybersecurity assessment. By simulating real-world attacks, they can identify and fix vulnerabilities before they can be exploited, giving you peace of mind knowing that your systems are secure. Whether it’s assessing security risks in your web applications, protecting user data on mobile apps, or evaluating the security of your network infrastructure, BreachLock has got you covered.
Certified by CREST and compliant with industry standards such as HIPAA, PCI DSS, ISO 27001, SOC 2, and GDPR, BreachLock offers a reliable and trustworthy solution. But don’t just take our word for it – their standardized built-in framework and AI-powered technology ensure faster vulnerability identification and accurate security testing. With enriched contextual insights and industry peer benchmarking, you can assess your security posture and make informed decisions to strengthen your defenses.
Features and Benefits
Comprehensive Applications Pentesting
Simulate real-world attacks on your software applications to identify and fix vulnerabilities before they can be exploited. With internal and external web app penetration testing, you can assess security risks and enhance the overall security posture of your web applications. Mobile app pentesting allows you to uncover security flaws and protect user data from malicious attackers. Additionally, thick client pentesting helps identify potential security weaknesses in desktop software apps.
Robust API Pentesting
Identify and address security vulnerabilities in APIs that enable different software applications to interact and exchange information. With internal and external API pentesting, BreachLock proactively discovers and fixes security flaws before they can be exploited, ensuring the integrity and security of your business-critical APIs.
Thorough Network Pentesting
Simulate real-world attacks on your network infrastructure to evaluate security vulnerabilities in network devices, systems, and applications. Internal and external network pentesting allows you to identify security weaknesses within your organization’s boundaries and external attack surface, providing valuable insights for enhancing your network security.
Secure Cloud Pentesting
Assess the security controls, configurations, and access mechanisms within hybrid and multi-cloud infrastructures, including popular platforms such as AWS, Azure, and GCP. Hybrid and multi-cloud pentesting ensures the identification of vulnerabilities in managing on-premises infrastructure and public cloud resources. With container and Kubernetes pentesting, you can rest assured that your containerized environments are secure and protected.
Complete DevOps Pentesting
Support your Secure Development Lifecycle by ensuring that your software is inherently secure and resilient to cyber threats. BreachLock’s DevOps pentesting services assess security across various phases of software development, including design, coding, testing, and deployment. By integrating security into your development process, you can mitigate vulnerabilities and bolster your overall cybersecurity posture.
Proactive IoT Pentesting
As the world becomes increasingly connected, securing IoT devices and systems is essential. BreachLock’s IoT pentesting services actively identify security weaknesses in interconnected IoT devices. By evaluating individual IoT device firmware, software, hardware, and communication protocols, they can uncover vulnerabilities and provide recommendations for strengthening your IoT security. Assessing the security of IoT cloud components, web interfaces, and supply chain processes ensures comprehensive protection against potential cyber threats.
Product Quality
BreachLock sets the standard for quality penetration testing services. Their expert team of certified professionals, combined with AI-powered technology, ensures accurate vulnerability identification and efficient security testing. Their comprehensive service offerings cover a wide range of cybersecurity domains, ensuring that your organization’s security is holistically evaluated.
Moreover, BreachLock is certified by CREST, a globally recognized organization that provides assurance and certification in the cybersecurity domain. This certification serves as a testament to the quality and reliability of BreachLock’s services. By adhering to industry standards such as HIPAA, PCI DSS, ISO 27001, SOC 2, and GDPR, BreachLock ensures that your organization stays compliant while maintaining a robust security posture.
What It’s Used For
Strengthen Applications Security
BreachLock’s applications pentesting services are designed to simulate real-world attacks on software applications. By proactively identifying and fixing vulnerabilities, they ensure that your applications remain secure and resilient to cyber threats. With web app penetration testing, mobile app pentesting, and thick client pentesting, they cover all types of software applications, providing a comprehensive assessment to enhance your organization’s security posture.
Secure APIs for Seamless Integration
APIs are crucial for enabling seamless interaction and data exchange between different software applications. However, they can also become potential vulnerabilities if not properly secured. BreachLock’s API pentesting services help identify and address security flaws in your APIs, ensuring that your systems remain secure while enabling the smooth integration of applications.
Enhance Network Security
Network security is of paramount importance in today’s interconnected world. BreachLock’s network pentesting services simulate real-world attacks on your network infrastructure, allowing you to evaluate security vulnerabilities in network devices, systems, and applications. By conducting both internal and external network pentesting, they uncover potential security weaknesses and provide actionable recommendations to enhance your organization’s network security.
Secure Cloud Environments
As more organizations adopt cloud technologies, securing cloud environments becomes critical. BreachLock’s cloud pentesting services assess the security controls, configurations, and access mechanisms within hybrid and multi-cloud infrastructures. By performing hybrid and multi-cloud pentesting, as well as container and Kubernetes pentesting, they help identify vulnerabilities in managing on-premises infrastructure and public cloud resources, ensuring the security of your entire cloud ecosystem.
Integrate Security into DevOps
DevOps environments require seamless collaboration between security operations and development teams. BreachLock’s DevOps pentesting services support your Secure Development Lifecycle by evaluating the security of your software across various phases of development. From design to coding, testing, and deployment, they help identify and mitigate vulnerabilities, enabling you to build inherently secure software and infrastructure.
Strengthen IoT Security
With the proliferation of IoT devices, securing interconnected systems becomes crucial. BreachLock’s IoT pentesting services actively identify security weaknesses in IoT devices and systems. By evaluating firmware, software, hardware, and communication protocols, as well as assessing IoT cloud components, web interfaces, and supply chain processes, they ensure that your IoT devices are secure and protected.

Product Specifications
| Specification | Details |
|---|---|
| Professional Certifications | CREST certified |
| Compliance | HIPAA, PCI DSS, ISO 27001, SOC 2, GDPR |
| Technology | AI-powered vulnerability identification |
| Integrations | Email alerts, JIRA, Jenkins, Trello, Slack, and more |
| Deliverables | CREST-certified reports, executive/board member reports |
| Services | Applications pentesting, API pentesting, network pentesting, cloud pentesting, DevOps pentesting, IoT pentesting |
| Pricing | Contact BreachLock for pricing details |
Who Needs This
Any organization that values the security of its digital assets should consider BreachLock’s penetration testing services. Whether you are a small business or a large enterprise, the comprehensive range of services offered by BreachLock ensures that your organization’s security is thoroughly assessed. From software application developers and network administrators to DevOps teams and IoT device manufacturers, anyone involved in the development, deployment, or management of digital assets can benefit from BreachLock’s expertise.
Pros and Cons
Pros:
- Human-delivered approach combined with AI-powered technology ensures accurate vulnerability identification.
- Comprehensive range of penetration testing services covering applications, APIs, networks, cloud environments, DevOps, and IoT.
- Certified by CREST and compliant with industry standards such as HIPAA, PCI DSS, ISO 27001, SOC 2, and GDPR.
- Enriched contextual insights and industry peer benchmarking provide valuable information for strengthening security defenses.
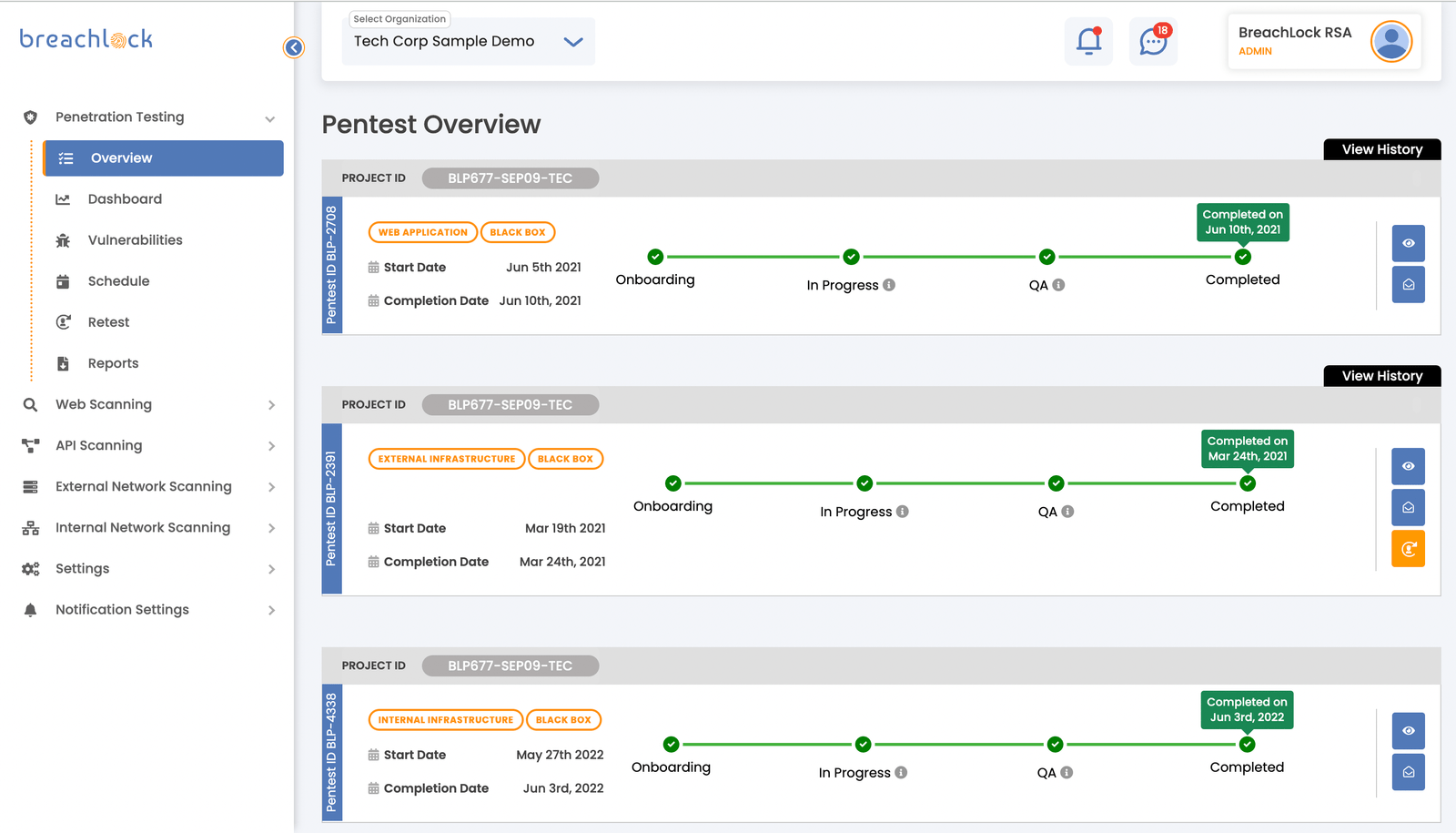
- BreachLock Enterprise Managed Services offer dedicated project managers, real-time result tracking, and unlimited retesting.
Cons:
- Pricing details are not publicly available and need to be obtained by contacting BreachLock directly.
- No information is provided regarding specific customer testimonials or case studies.
FAQ’s
Q: What is penetration testing? A: Penetration testing involves simulating real-world attacks on your digital assets to identify vulnerabilities before they can be exploited. It helps organizations assess the security of their applications, networks, and systems.
Q: How does BreachLock ensure accurate vulnerability identification? A: BreachLock combines human expertise with AI-powered technology to ensure accurate and efficient vulnerability identification. Their experts perform manual testing while leveraging AI capabilities for faster and more accurate results.
Q: Can BreachLock help with compliance requirements? A: Yes, BreachLock’s services are designed to help organizations achieve compliance with industry standards such as HIPAA, PCI DSS, ISO 27001, SOC 2, and GDPR. By identifying and addressing security vulnerabilities, they assist in meeting regulatory requirements.
Q: Can BreachLock provide support throughout the entire penetration testing process? A: Yes, BreachLock’s Enterprise Managed Services offer dedicated project managers, real-time result tracking, remediation experts, unlimited retesting, and unlimited ticket creation. They provide end-to-end support from initial assessment to final remediation.
What Customers Are Saying
“While working with BreachLock, we were impressed with their expertise and professionalism. Their penetration testing services helped us identify and fix vulnerabilities, ensuring the security of our digital assets. We highly recommend their services.”
“BreachLock’s comprehensive range of penetration testing services has been instrumental in strengthening our organization’s security defenses. Their insights and recommendations have helped us mitigate potential risks and enhance our overall security posture.”
Overall Value
BreachLock offers comprehensive, reliable, and effective penetration testing services that provide exceptional value for organizations looking to enhance their security defenses. With their human-delivered approach, AI-powered technology, and industry certifications, they ensure accurate vulnerability identification and help address compliance requirements. The comprehensive range of services covers all aspects of cybersecurity, from applications and networks to cloud environments, DevOps, and IoT. With BreachLock, you can protect your digital assets and stay one step ahead of potential cyberattacks.
Tips and Tricks For Best Results
- Prioritize regular penetration testing: Conducting regular penetration tests ensures that your systems remain secure and up-to-date. Schedule tests at regular intervals to identify vulnerabilities and address them promptly.
- Collaborate with your development teams: Integrate security into your DevOps process by fostering collaboration between security operations and development teams. This ensures that security is considered at every stage of software development.
- Stay up-to-date with industry standards: Maintain compliance with industry standards such as HIPAA, PCI DSS, ISO 27001, SOC 2, and GDPR. Regularly review and update your security practices to meet evolving compliance requirements.
- Act on vulnerabilities promptly: When vulnerabilities are identified, prioritize remediation efforts to minimize the risk of exploitation. Work closely with your internal teams or engage BreachLock’s remediation experts for effective vulnerability fixes.
- Leverage integration options: Take advantage of BreachLock’s integration options, such as email alerts, JIRA, Jenkins, Trello, and Slack. These integrations allow you to receive real-time results and facilitate collaboration between teams.
Final Thoughts
Product Summary
BreachLock’s Human-Delivered Penetration Testing Services are designed to help organizations protect their digital assets by identifying and fixing vulnerabilities before they can be exploited. With a combination of human expertise and AI-powered technology, BreachLock ensures accurate vulnerability identification and provides comprehensive insights for enhancing your security defenses. Their services cover applications, APIs, networks, cloud environments, DevOps, and IoT, ensuring that all aspects of your organization’s security are thoroughly evaluated.
Final Recommendation
If you’re looking for comprehensive, reliable, and effective penetration testing services, BreachLock is the ideal choice. With their human-delivered approach and AI-powered technology, they provide accurate vulnerability identification, enabling you to safeguard your organization from potential cyberattacks. Certified by CREST and compliant with industry standards, BreachLock offers a trustworthy solution for assessing and enhancing your security defenses. Choose BreachLock today to protect your digital assets and stay one step ahead of potential threats. Contact them to learn more and start strengthening your organization’s security.















