Building Complete AI Security Solutions: Your Comprehensive Implementation Guide
Building complete AI security solutions requires the integration of diverse technologies, processes, and organizational capabilities into comprehensive frameworks that can protect against current threats while adapting to emerging challenges. Throughout…
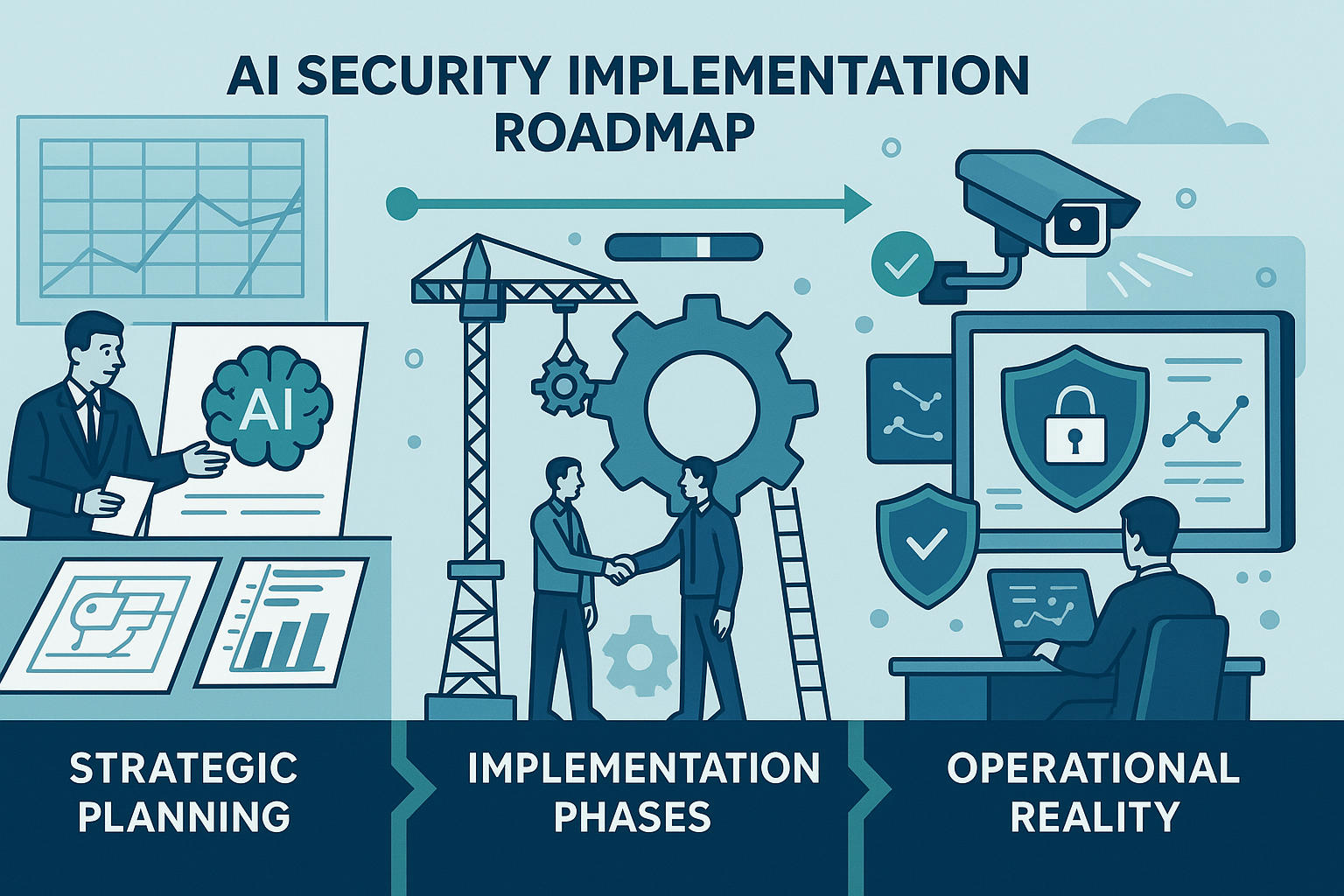
Implementing AI Security Solutions: From Strategy to Operational Reality
The transition from AI security strategy to operational implementation represents one of the most critical and challenging phases in building comprehensive protection for enterprise AI systems. While understanding AI security…
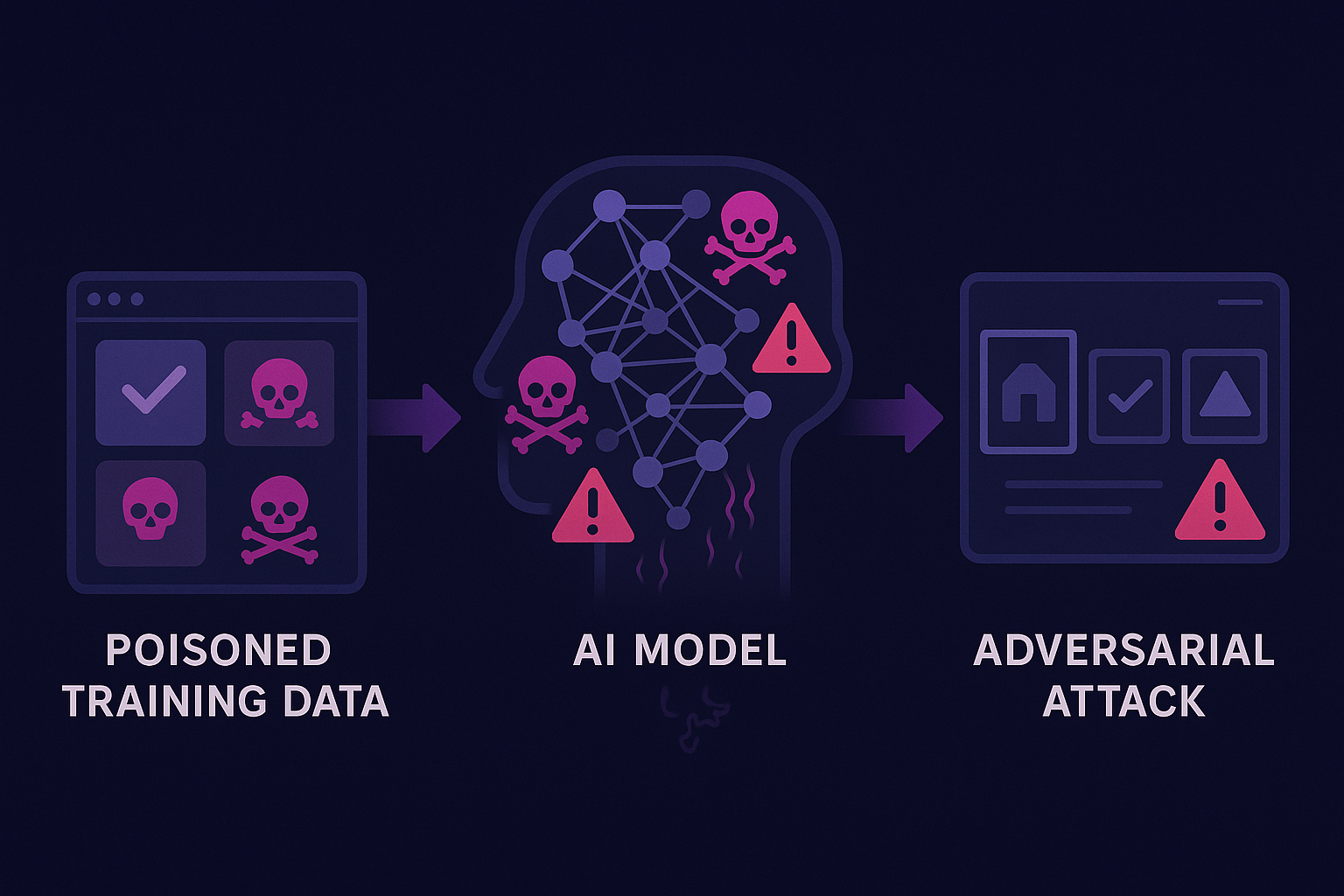
AI Model Poisoning and Adversarial Attacks: Corrupting Intelligence at the Source
AI model poisoning and adversarial attacks represent some of the most sophisticated and potentially devastating threats facing modern artificial intelligence systems. Unlike prompt injection attacks that target AI systems through…
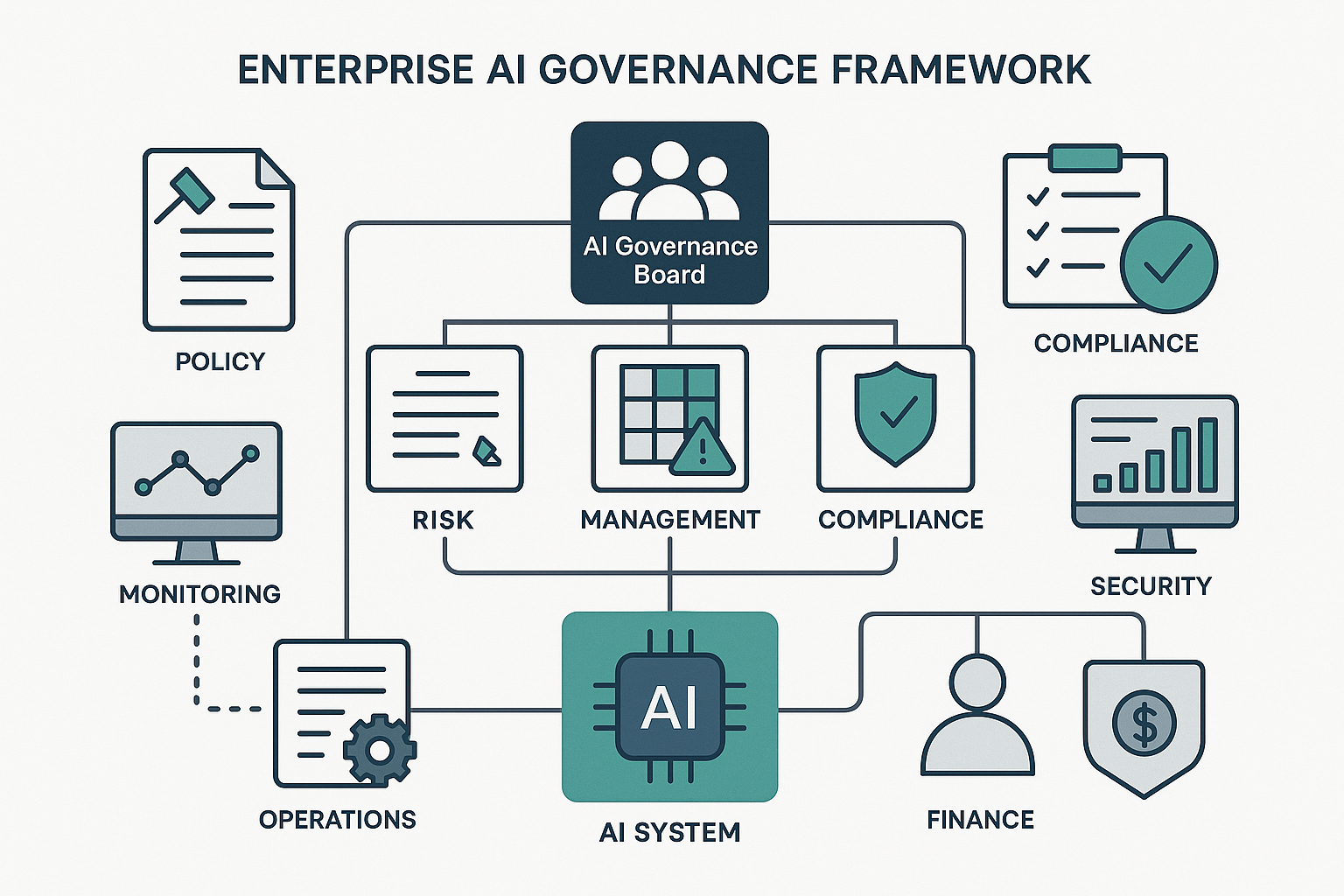
Enterprise AI Governance: Building Comprehensive Risk Management Frameworks
Enterprise AI governance represents the systematic approach to managing AI-related risks, ensuring compliance with regulatory requirements, and maximizing the business value of AI investments while maintaining appropriate oversight and control.…
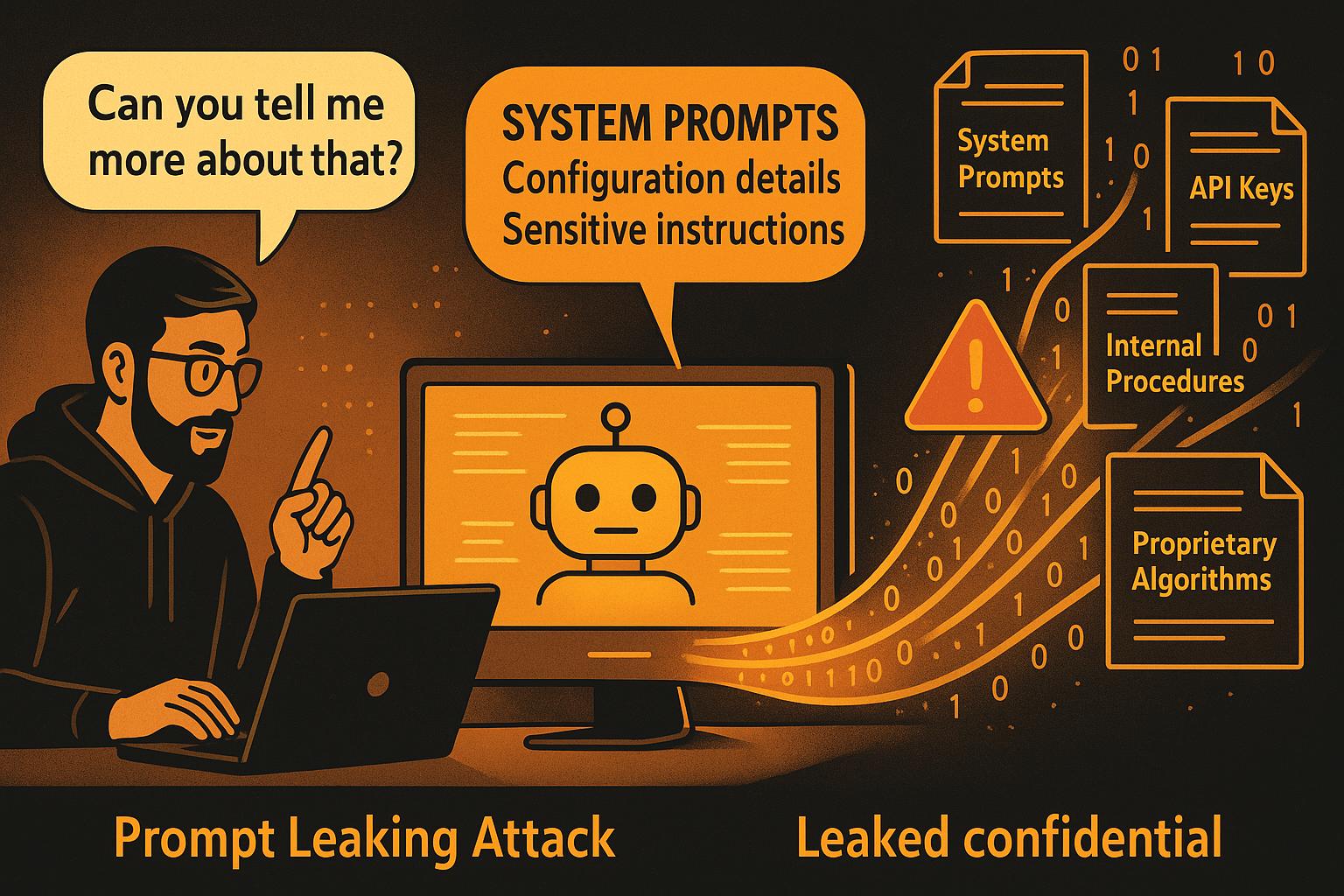
Prompt Leaking Attacks: When AI Systems Reveal Their Secrets
Prompt leaking attacks represent a specialized and particularly dangerous form of AI security threat that specifically targets the extraction of sensitive system prompts, configuration details, and proprietary information from AI…
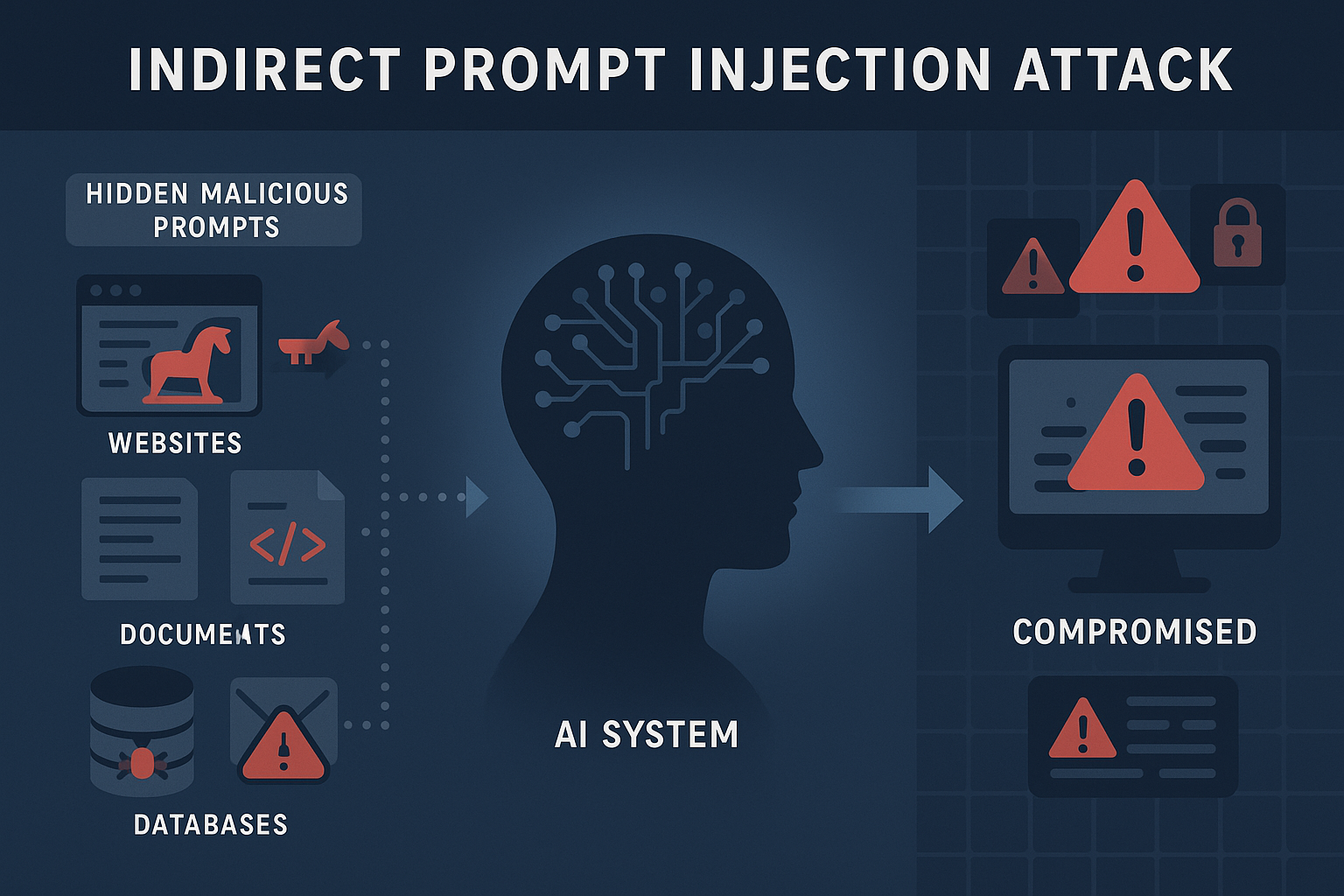
Indirect Prompt Injection: The Hidden Threat Lurking in Your Data Sources
Indirect prompt injection attacks represent one of the most insidious and difficult-to-detect threats facing modern AI systems. Unlike direct prompt injection attacks that involve explicit manipulation attempts through user inputs,…
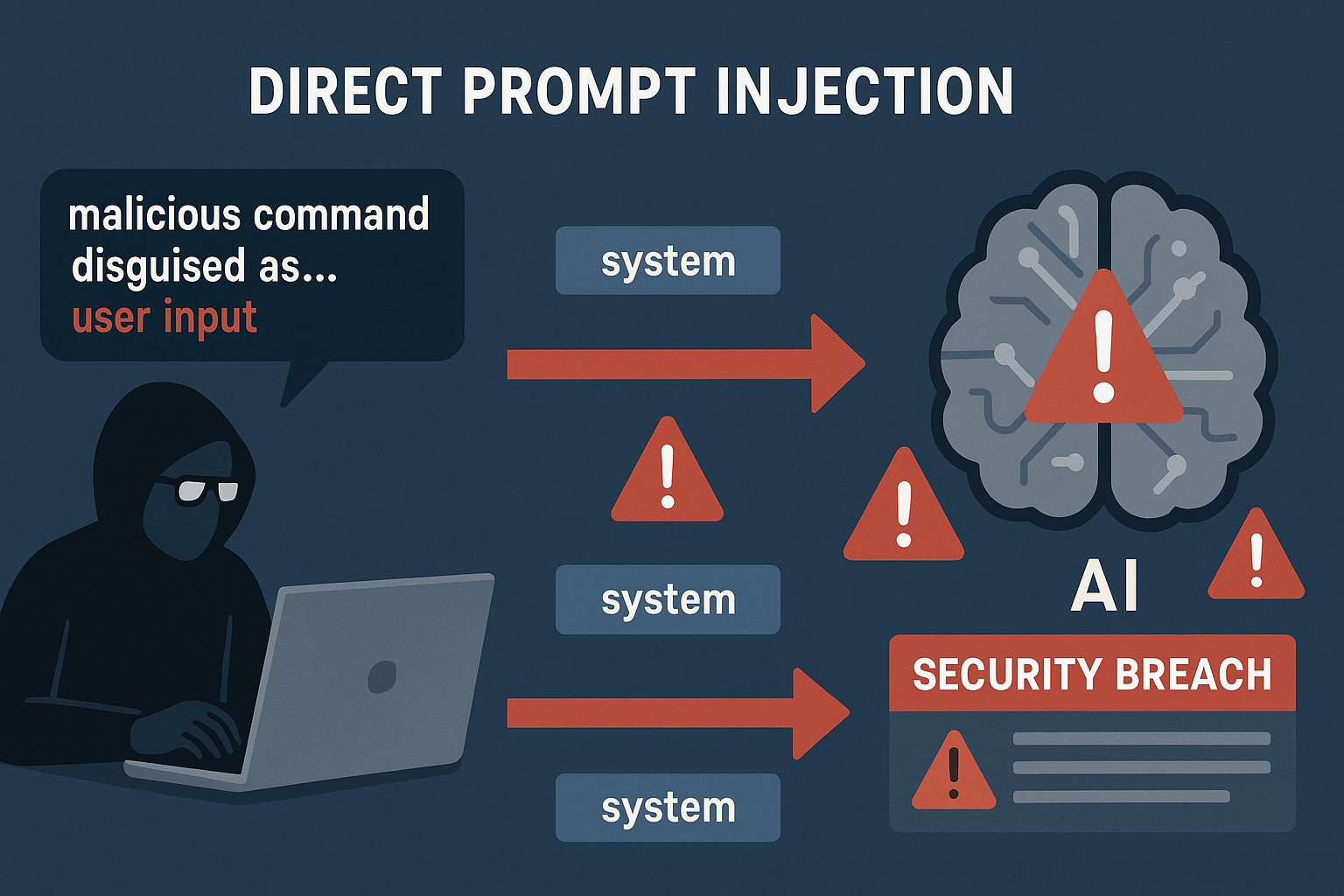
Direct Prompt Injection Attacks: How Hackers Manipulate AI Systems Through Clever Commands
Direct prompt injection attacks represent the most immediate and widespread threat facing AI systems deployed in enterprise environments today. These attacks exploit the fundamental architecture of modern AI systems by…
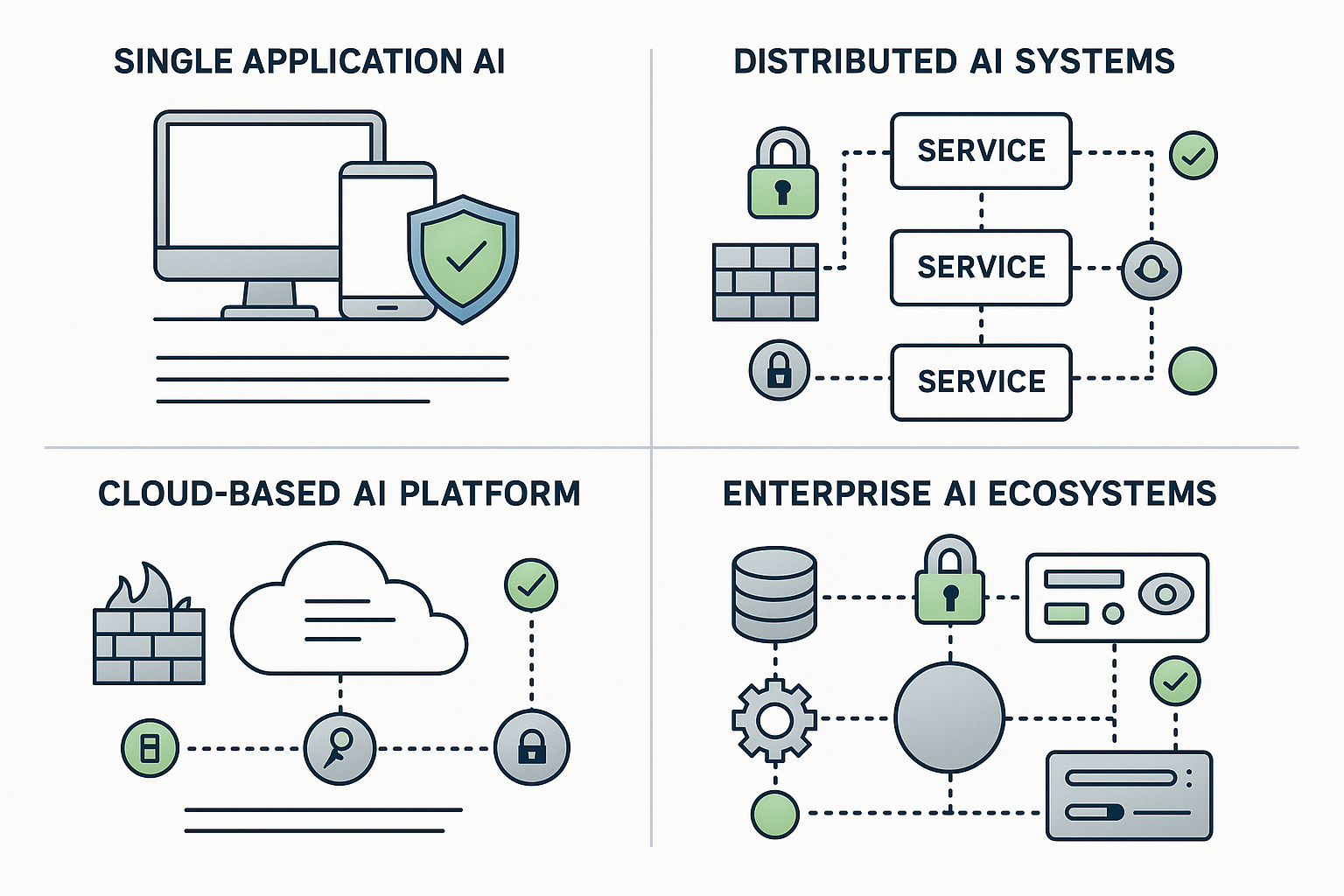
Understanding AI Software Architecture: Security Implications of Different Deployment Models
The security posture of artificial intelligence systems is fundamentally determined by their underlying architecture and deployment model. As organizations increasingly integrate AI capabilities into their operations, understanding the security implications…