What looks like a routine CAPTCHA or browser fix prompt may actually be the first step in a malware infection. ClickFix attacks are evolving into a highly effective social-engineering technique that uses compromised WordPress sites, fake verification pages, and Windows-native tools to trick users into launching malware themselves. 
ClickFix Is No Longer a Simple Scam
For years, cybercriminals have relied on one timeless advantage: people trust what feels familiar. ClickFix attacks exploit that instinct by presenting users with what looks like a routine step—verifying a CAPTCHA, fixing a browser issue, or clearing a security warning—then tricking them into running malicious commands themselves.
What began as a relatively simple lure has evolved into something much more dangerous. Modern ClickFix campaigns now combine polished social engineering with automated infrastructure, compromised websites, clipboard manipulation, fileless malware execution, and payloads specifically designed to evade analysis.
That shift matters because it changes ClickFix from a nuisance into a serious business and consumer threat. It is no longer just about getting someone to click a bad link. It is about convincing them to become the final step in their own infection chain.
The most dangerous part of ClickFix is that the victim often executes the malware themselves.
Why ClickFix Attacks Are Spreading So Quickly
The reason ClickFix is thriving is simple: it works. Security researchers have documented a sharp rise in ClickFix-style activity, with campaigns increasingly using fake CAPTCHA prompts, browser error messages, and consent-themed lures to lower a victim’s guard. Instead of relying on traditional exploit chains, attackers are bypassing technical friction by exploiting normal user behavior. That makes these campaigns both cheap and effective. A fake verification page is easier to deploy than a zero-day exploit, and if the victim willingly opens PowerShell or Windows Terminal, many traditional controls are already at a disadvantage. This is also why ClickFix has become attractive to a wide range of operators. It is flexible, low-cost, and easy to adapt across malware families.
Why ClickFix Social Engineering Is So Effective
ClickFix works because it mimics expected behavior. Users are used to clicking “I’m not a robot,” dismissing browser warnings, or following troubleshooting instructions. Attackers wrap malicious instructions inside that same familiar experience. The user does not feel like they are bypassing security. They feel like they are completing a harmless step.
How the Modern ClickFix Attack Chain Works
Today’s ClickFix campaigns are often multi-stage operations rather than one-off scams.
A victim may land on a compromised website, a phishing page, or a malicious ad. The page then displays a fake prompt—often styled to look like Cloudflare, Google reCAPTCHA, or a browser system message. In many cases, the user is told to click a button, which silently copies a malicious command to the clipboard.
Next comes the social-engineering payoff: the site instructs the victim to open Run, PowerShell, or Windows Terminal and paste the command. Once that happens, the malware chain begins.
This structure is powerful because it offloads execution to the target. Rather than forcing malware onto a machine through a noisy exploit, the attacker persuades the user to launch it voluntarily.
ClickFix does not just trick users into clicking. It tricks them into executing.
The fake CAPTCHA is only the beginning. Behind the prompt, the attack may involve obfuscated JavaScript, clipboard poisoning, remote payload retrieval, PowerShell stagers, shellcode loaders, and in-memory injection into legitimate Windows processes. That means what looks like a harmless browser prompt can quickly become a full infostealer infection.

The WordPress Angle: Trusted Sites as Attack Infrastructure
One of the most alarming developments in recent reporting is the use of compromised WordPress sites as ClickFix delivery platforms. This is a major escalation because it solves one of phishing’s oldest problems: trust. Attackers no longer need to lure users only to suspicious-looking domains. By compromising legitimate WordPress sites—including business pages, local media outlets, and other trusted properties—they can deliver malicious prompts from domains that already appear credible. That dramatically increases the odds that a user will believe the prompt is real.
Compromised WordPress Sites Used in ClickFix Attacks
In these campaigns, attackers inject malicious JavaScript into WordPress pages and selectively display fake human-verification prompts to visitors. Some operations are designed to avoid showing the prompt to site administrators, helping the compromise remain hidden for longer. That selective visibility is an important sign of maturity. It shows that attackers are thinking beyond initial compromise and focusing on persistence, stealth, and campaign longevity.
Stealth Has Become a Core Part of the Playbook
Modern ClickFix infrastructure is not just convincing. It is intentionally difficult to detect. Attackers increasingly use remote lure content, centralized command infrastructure, obfuscated scripts, and malware that runs largely in memory. This reduces the number of obvious files dropped to disk and makes traditional signature-based defenses less reliable. Some payloads also include sandbox detection, timing checks, encrypted command-and-control traffic, and dead-drop style configuration retrieval. In plain terms, the malware is built not only to steal information, but to resist analysis while doing it.
The lure may look simple, but the backend delivery chain is increasingly professionalized.
From Run Dialog to Windows Terminal: Why the Tactic Keeps Adapting
A notable shift in recent campaigns is the move from classic Win+R execution prompts to instructions involving Windows Terminal and PowerShell. This might seem minor, but it reflects how quickly social engineering evolves. Attackers are constantly testing which interfaces feel normal enough to users to avoid suspicion. Windows Terminal can appear more modern, more legitimate, and less alarming than older execution methods. The lesson is clear: ClickFix is not tied to one prompt or one Windows feature. It is a reusable deception model. If users become wary of one interface, attackers simply repackage the same tactic in another.
ClickFix Attacks Using Windows Terminal and PowerShell
This flexibility is part of what makes ClickFix dangerous. It is not a single malware family or a fixed exploit chain. It is an adaptable delivery technique that can carry many different payloads depending on the operator’s goals.
The Malware Behind ClickFix: Infostealers, RATs, and More
ClickFix campaigns are often used to deliver infostealers, remote access trojans, and downloaders that enable follow-on compromise. Some operations rely on established families like Vidar or Lumma, while others introduce newer or less documented payloads. The target set usually includes browser credentials, session tokens, cryptocurrency wallets, saved passwords, and other high-value data that can be monetized quickly. This makes ClickFix especially attractive to financially motivated groups. It provides a reliable front-end deception layer for malware that is already proven to generate profit.
What Malware Does ClickFix Deliver?
The answer varies, but infostealers remain the most common and damaging class. Once installed, these tools can harvest credentials, exfiltrate browsing data, steal wallet information, and create opportunities for account takeover, business email compromise, or broader intrusion. That means even a single successful ClickFix event can lead to much larger downstream damage.
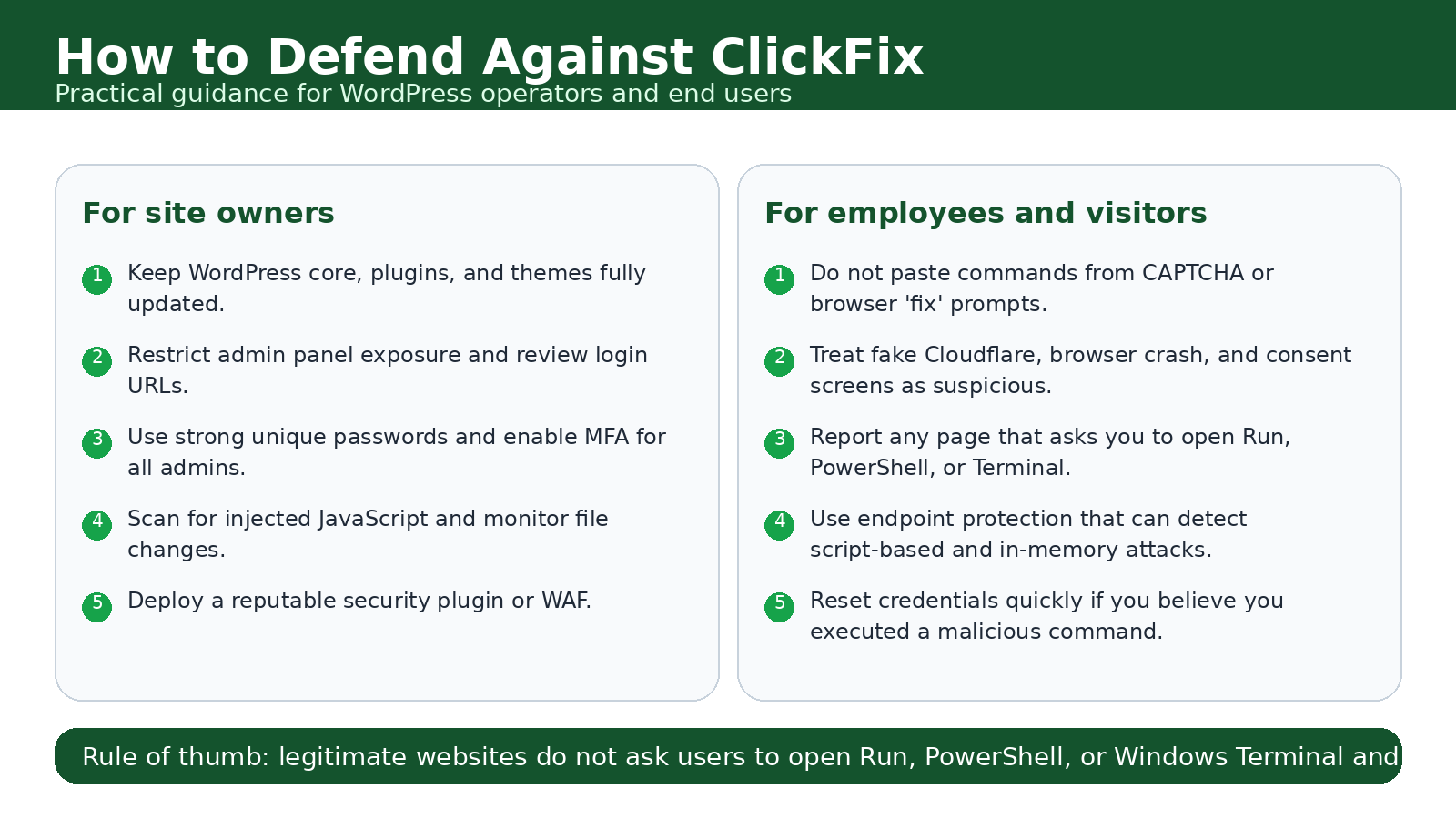
What WordPress Site Owners Should Do Right Now
For WordPress operators, the risk is not just being hacked—it is becoming an unwilling distributor of malware to visitors. That makes prevention and monitoring equally important. Keep WordPress core, plugins, and themes updated. Remove anything unnecessary. Restrict admin access where possible. Enforce strong, unique passwords and multi-factor authentication. Monitor for unauthorized JavaScript changes and suspicious redirects. Review plugin integrity and minimize exposure of administrative interfaces. A compromised website can damage more than your SEO or uptime. It can damage user trust, spread malware, and expose your organization to reputational and legal fallout.
A hacked WordPress site is no longer just a defacement risk. It can become an active malware distribution node.
How to Protect Against ClickFix Attacks
The defensive advice here is refreshingly direct. A legitimate website should never tell you to open Run, PowerShell, Command Prompt, or Windows Terminal and paste a command to verify yourself, fix a browser issue, or continue to content. That instruction alone should be treated as a red flag. For organizations, employee awareness training should explicitly cover fake CAPTCHA attacks, browser fix scams, and verification prompts that involve system tools. Detection engineering should also focus on suspicious PowerShell usage, unusual clipboard-to-command execution patterns, and child processes spawned from user-driven scripting tools. The best defense is a combination of user skepticism and technical visibility. Train users not to paste commands from websites. Harden WordPress and other public-facing systems. Monitor for script-based execution. Use endpoint tools capable of catching in-memory and LOLBin-assisted attacks. Stopping the user from performing that one final step is often enough to break the entire chain.
How to Spot a ClickFix Prompt
- A website tells you to open Run, PowerShell, Command Prompt, or Windows Terminal.
- You are instructed to copy and paste a command to “verify,” “fix,” or “continue.”
- The prompt imitates a trusted service such as Cloudflare, a CAPTCHA provider, or a browser warning.
- The message creates urgency by claiming your browser crashed, your session expired, or your access is blocked.
- A supposed verification step requires actions that have nothing to do with normal web browsing.
Rule of thumb: legitimate websites do not ask users to paste system commands to prove they are human.
Final Takeaway: ClickFix Is an Evolution in Human-Led Intrusion
ClickFix matters because it represents a broader shift in cybercrime. Attackers are investing less in flashy technical exploits and more in polished, believable experiences that persuade people to do the dangerous part for them. That is what makes the latest wave so effective. The fake CAPTCHA is not the real attack. The real attack is the moment the victim trusts it. As ClickFix continues to evolve through compromised WordPress sites, stealthier loaders, and more flexible execution paths, defenders need to treat it as more than a phishing variation. It is now a mature social-engineering delivery framework—one that thrives at the intersection of trust, habit, and automation.










