Building complete AI security solutions requires the integration of diverse technologies, processes, and organizational capabilities into comprehensive frameworks that can protect against current threats while adapting to emerging challenges. Throughout this series, we have explored the complex landscape of AI security threats, examined advanced defensive technologies, and analyzed implementation strategies that organizations can use to build robust protection for their AI systems. This final article synthesizes these insights into practical guidance for creating comprehensive AI security solutions that address the full spectrum of AI security challenges.
The journey from understanding AI security threats to implementing complete security solutions represents a significant undertaking that requires sustained commitment, substantial investment, and ongoing adaptation to evolving threat landscapes. Organizations that successfully build comprehensive AI security capabilities will be better positioned to realize the benefits of AI technology while maintaining the trust and confidence of stakeholders who depend on the security and reliability of AI-powered systems and services.
The business imperative for comprehensive AI security has never been more urgent as organizations become increasingly dependent on AI systems for critical business functions while facing sophisticated threats that can undermine the integrity, availability, and confidentiality of AI systems. Complete AI security solutions provide the foundation for sustainable AI adoption that can deliver business value while managing risks appropriately and maintaining stakeholder confidence in organizational AI capabilities.
Synthesis of AI Security Fundamentals
The foundation of complete AI security solutions lies in understanding the unique characteristics of AI systems that create both opportunities and vulnerabilities that differ fundamentally from traditional information systems. AI systems process vast amounts of data, make autonomous decisions, learn and adapt over time, and operate in complex environments that create novel attack vectors and defensive requirements that must be addressed through specialized security approaches.
The four types of prompt injection attacks that we examined in detail represent just one category of AI-specific threats that organizations must address through comprehensive security frameworks. Direct prompt injection attacks exploit the conversational interfaces of AI systems through malicious user inputs, while indirect attacks leverage contaminated data sources to influence AI behavior. Stored prompt injection attacks target the data repositories that AI systems use for context and decision-making, while prompt leaking attacks seek to extract sensitive information about AI system configuration and capabilities.
Model poisoning and adversarial attacks target the fundamental intelligence of AI systems by corrupting training data or crafting malicious inputs that cause AI systems to behave inappropriately. These attacks can have persistent effects that compromise AI system reliability and trustworthiness while being extremely difficult to detect and remediate. Understanding these attack mechanisms is essential for developing effective defensive strategies that can protect AI systems throughout their operational lifecycles.
The enterprise implications of AI security threats extend far beyond immediate technical concerns to encompass business continuity, competitive advantage, regulatory compliance, and stakeholder trust. AI security failures can result in operational disruption, financial losses, regulatory penalties, reputational damage, and erosion of competitive advantages that organizations have built through their AI investments. Comprehensive security solutions must address these business implications while enabling organizations to realize the full potential of AI technology.
The evolution of AI security threats continues to accelerate as attackers develop more sophisticated techniques and as AI systems become more complex and widely deployed. Organizations must build security capabilities that can adapt to evolving threats while maintaining effectiveness against current attack techniques. This requires security frameworks that combine proven defensive approaches with emerging technologies and continuous improvement processes that can address new challenges as they emerge.
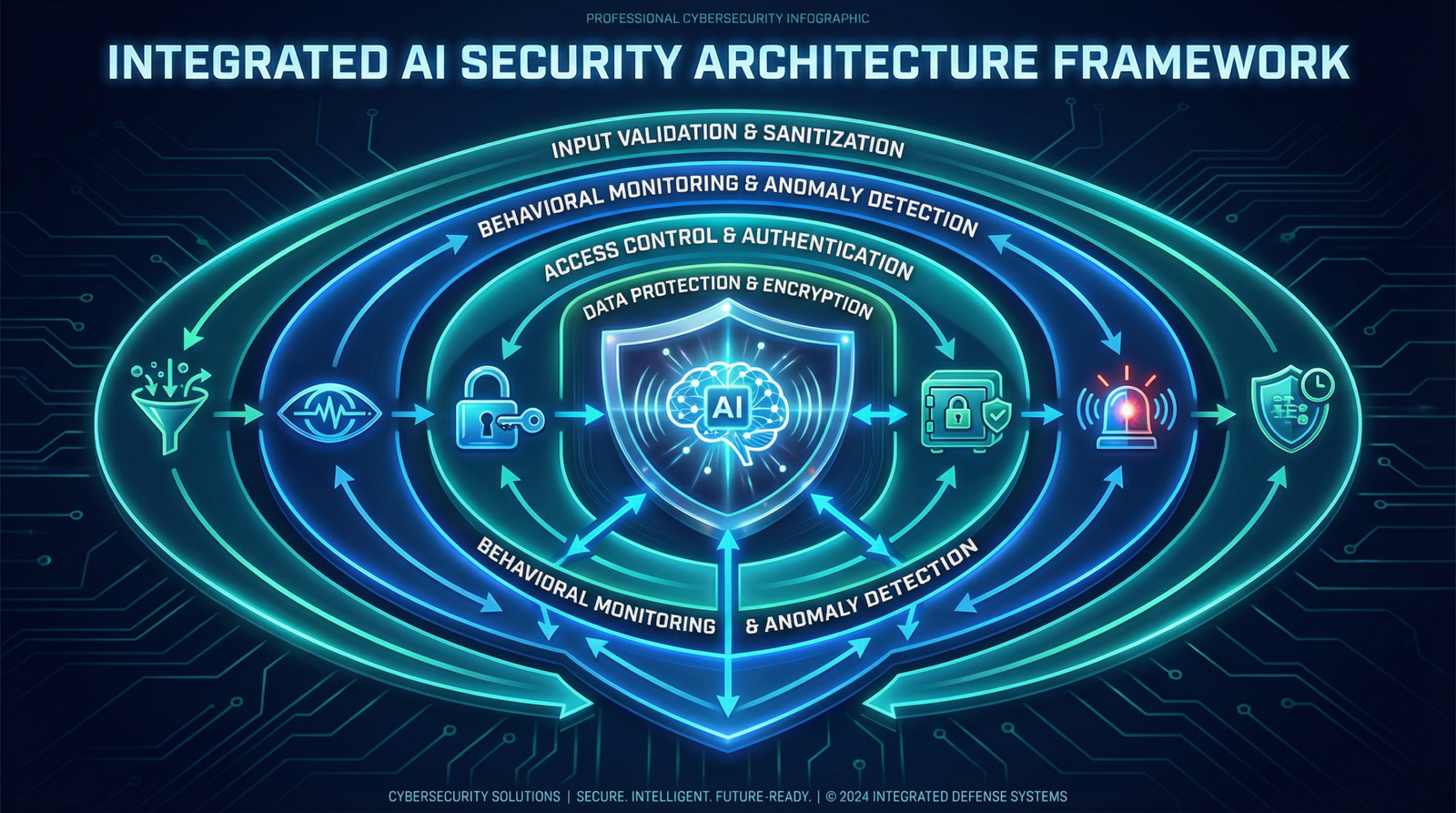
Integrated Security Architecture Framework
Complete AI security solutions require integrated architectures that address threats at multiple levels including input validation, behavioral monitoring, access control, data protection, and incident response. These architectures must provide defense-in-depth protection that can prevent, detect, and respond to diverse types of AI security threats while maintaining the performance and functionality that make AI systems valuable for business operations.
Input validation and sanitization systems form the first line of defense in AI security architectures by analyzing and filtering inputs before they reach AI processing systems. Validation systems must be sophisticated enough to detect subtle manipulation attempts while being efficient enough to handle the large volumes of inputs that modern AI systems process. Input validation must address diverse input types including text, images, audio, and structured data while providing appropriate fallback mechanisms when suspicious inputs are detected.
The technical implementation of input validation requires multiple detection techniques including pattern-based analysis, semantic evaluation, statistical anomaly detection, and machine learning-based classification. Validation systems must be continuously updated to address new attack techniques while maintaining low false positive rates that do not interfere with legitimate system usage. Input validation must be integrated with broader security monitoring and response systems to provide coordinated threat detection and response.
Behavioral monitoring and anomaly detection provide ongoing oversight of AI system behavior to identify potential security threats, system malfunctions, or policy violations. Monitoring systems must establish baselines of normal AI behavior while identifying deviations that may indicate compromise or inappropriate operation. Behavioral monitoring must address both technical performance metrics and business-relevant behaviors while providing real-time alerting capabilities that enable rapid response to detected anomalies.
Access control and authentication mechanisms ensure that only authorized users and systems can interact with AI capabilities while providing appropriate granularity for different types of AI resources and operations. Access control for AI systems must address both human users and automated systems while providing fine-grained permissions that can distinguish between different types of AI interactions. Authentication must be strong enough to prevent unauthorized access while being efficient enough to support high-volume AI operations.
Data protection and encryption throughout the AI lifecycle ensure that sensitive information is protected at all stages of AI processing including data collection, storage, training, inference, and output delivery. Data protection must address both data at rest and data in transit while providing appropriate key management and access controls. Encryption must be implemented in ways that do not significantly impact AI system performance while providing strong protection against unauthorized access and tampering.
Incident response and recovery capabilities enable rapid detection, analysis, and remediation of AI security incidents while minimizing their impact on business operations. Incident response for AI systems must address the unique characteristics of AI security threats while integrating with broader organizational incident response processes. Recovery capabilities must include procedures for restoring AI systems to secure and functional states while preserving evidence for investigation and lessons learned.
Governance and Risk Management Integration
Complete AI security solutions require comprehensive governance frameworks that provide oversight, accountability, and continuous improvement for AI security activities. Governance frameworks must address the unique characteristics of AI systems while integrating with existing organizational governance, risk management, and compliance processes to provide coherent and effective oversight of AI security risks and opportunities.
AI governance structures must include appropriate organizational roles and responsibilities for AI security oversight including executive leadership, technical teams, business units, and specialized functions such as risk management, compliance, and ethics. Governance structures must provide clear accountability for AI security decisions while enabling effective coordination between diverse organizational functions that are involved in AI development, deployment, and operation.
Risk assessment and management processes for AI systems must address both technical risks related to AI system behavior and broader business risks related to AI deployment and operation. Risk assessment must consider factors such as data sensitivity, decision-making authority, business criticality, and exposure to external threats while providing appropriate prioritization and mitigation strategies. Risk management must be ongoing throughout the AI lifecycle rather than being limited to initial deployment decisions.
Policy development and enforcement ensure that AI security requirements are clearly defined and consistently applied across the organization. Policies must address AI development practices, deployment requirements, operational procedures, and incident response protocols while providing appropriate flexibility for different types of AI applications and business contexts. Policy enforcement must be automated where possible while providing appropriate oversight and exception handling mechanisms.
Compliance management addresses the evolving regulatory landscape for AI systems while ensuring that organizational AI activities meet applicable legal and regulatory requirements. Compliance management must monitor regulatory developments while assessing their impact on organizational AI activities and implementing appropriate compliance measures. Compliance frameworks must address diverse regulatory requirements including data protection, algorithmic accountability, and industry-specific regulations.
Performance measurement and continuous improvement processes ensure that AI security capabilities continue to evolve and improve based on operational experience, changing requirements, and emerging threats. Performance measurement must address both technical security metrics and business-relevant outcomes while providing data-driven insights for security improvement decisions. Continuous improvement must be systematic and must involve all stakeholders in the AI security ecosystem.
Technology Implementation and Integration
The technical implementation of complete AI security solutions requires careful selection and integration of diverse security technologies that can provide comprehensive protection while maintaining compatibility with existing enterprise infrastructure and AI systems. Technology implementation must address both immediate security needs and long-term evolution requirements while providing appropriate scalability and performance characteristics.
Security tool selection and evaluation must consider factors such as functional capabilities, integration requirements, performance characteristics, vendor viability, and total cost of ownership. Tool selection must address the diverse types of AI security threats while providing appropriate coverage for different AI applications and deployment environments. Evaluation processes must include proof-of-concept testing and pilot implementations that can assess tool effectiveness in realistic operational environments.
Integration architecture design must address the complex requirements of connecting diverse security tools and systems while providing seamless security coverage across AI applications and infrastructure. Integration must address data sharing, workflow coordination, and management interfaces while maintaining security and performance requirements. Architecture design must consider both current integration needs and future evolution requirements as security capabilities and AI systems continue to develop.
Deployment and operational transition processes ensure that AI security technologies are implemented successfully and begin providing effective protection without disrupting existing operations. Deployment must include comprehensive testing, staged rollout procedures, and performance optimization activities that ensure security solutions are functioning correctly and efficiently. Operational transition must include training, documentation, and support processes that enable effective ongoing management of security capabilities.
Monitoring and optimization activities ensure that deployed AI security solutions continue to perform effectively while identifying opportunities for improvement and enhancement. Monitoring must address both security effectiveness metrics and operational performance characteristics while providing insights for optimization decisions. Optimization must balance security effectiveness with operational efficiency while maintaining appropriate levels of protection.
Organizational Capability Development
Building complete AI security solutions requires significant investment in organizational capabilities including specialized expertise, cross-functional collaboration, and cultural adaptation to address the unique requirements and challenges of AI security. Capability development must address both technical skills and broader organizational competencies that are needed to implement and manage comprehensive AI security programs.
Security team development and training programs must provide cybersecurity professionals with the specialized knowledge and skills needed to understand and address AI security threats. Training must cover AI system architecture, attack techniques, defensive strategies, and incident response procedures while building on existing cybersecurity expertise. Training programs must be ongoing to address the rapidly evolving nature of AI security threats and defensive technologies.
Cross-functional collaboration and coordination mechanisms ensure that AI security implementation involves appropriate stakeholders from across the organization while providing effective communication and decision-making processes. Collaboration must address the diverse perspectives and requirements of different organizational functions while maintaining focus on security objectives and business outcomes. Coordination mechanisms must provide clear roles and responsibilities while enabling flexible adaptation to changing requirements and circumstances.
Process development and documentation activities establish the operational procedures needed to implement and manage AI security solutions effectively. Process development must address AI security governance, risk assessment, incident response, compliance management, and continuous improvement activities while integrating with existing organizational processes. Documentation must provide clear guidance for implementation teams while ensuring that processes can be consistently applied across the organization.
Cultural change and awareness programs help organizations adapt to the unique requirements and challenges of AI security while building support for security initiatives across the organization. Awareness programs must educate stakeholders about AI security risks, the importance of security measures, and their roles in maintaining effective protection. Cultural change initiatives must address resistance to new security requirements while building understanding of the business value of AI security investments.
Vendor and partner management processes address the unique challenges of implementing AI security solutions that may involve external vendors, service providers, or technology partners. Vendor management must address security requirements for AI security tools and services while ensuring appropriate integration and support capabilities. Partner management must ensure that external relationships support rather than compromise AI security objectives while providing appropriate oversight and accountability.
Continuous Improvement and Evolution
Complete AI security solutions must be designed for continuous improvement and evolution to address the rapidly changing landscape of AI security threats and defensive technologies. Improvement processes must be systematic and must involve all stakeholders in identifying opportunities for enhancement while implementing changes that improve security effectiveness without disrupting ongoing operations.
Performance measurement and analytics provide the foundation for continuous improvement by tracking key performance indicators that assess both security effectiveness and business outcomes. Measurement must address technical metrics such as threat detection rates and response times as well as business metrics such as incident impact and stakeholder satisfaction. Analytics must provide insights that can guide improvement decisions while identifying trends and patterns that may indicate emerging challenges or opportunities.
Threat intelligence integration ensures that AI security solutions remain current with evolving threat landscapes while adapting to new attack techniques and emerging vulnerabilities. Threat intelligence must be collected from diverse sources including commercial providers, government agencies, industry organizations, and internal security research. Intelligence integration must be automated where possible while providing appropriate analysis and contextualization that can guide security improvement decisions.
Technology evolution and upgrade planning address the need to continuously enhance AI security capabilities as new technologies become available and as existing technologies mature and improve. Evolution planning must balance the benefits of new technologies with the costs and risks of change while maintaining continuity of protection during transition periods. Upgrade planning must consider both incremental improvements and more significant technology transitions that may be needed to address emerging threats or requirements.
Lessons learned and knowledge management activities capture insights from AI security implementation experiences while making them available for future improvement efforts and organizational learning. Lessons learned must address both successful practices that should be replicated and challenges that should be avoided or mitigated in future implementations. Knowledge management must ensure that implementation insights are preserved and shared effectively across the organization while contributing to broader industry knowledge and best practices.
Stakeholder feedback and engagement processes provide ongoing input from various stakeholders about AI security effectiveness, emerging concerns, and improvement opportunities. Feedback must be systematically collected and analyzed while being incorporated into improvement planning and implementation activities. Engagement processes must demonstrate that stakeholder input is valued and acted upon while building ongoing support for AI security initiatives.
Conclusion: Your Path to AI Security Excellence
Building complete AI security solutions represents one of the most important investments that organizations can make in their AI capabilities and business futures. The comprehensive approach outlined in this series provides a roadmap for developing AI security capabilities that can protect against current threats while adapting to emerging challenges and evolving business requirements.
The key to success lies in recognizing that AI security is not a destination but rather an ongoing journey that requires sustained commitment, continuous learning, and adaptive improvement. Organizations that approach AI security systematically and invest in comprehensive capabilities will be better positioned to realize the full potential of AI technology while maintaining the trust and confidence of stakeholders who depend on the security and reliability of AI systems.
The business benefits of comprehensive AI security extend far beyond immediate threat protection to encompass competitive advantage, stakeholder confidence, regulatory compliance, and the ability to innovate safely and responsibly with AI technology. Organizations that build complete AI security solutions will be better equipped to thrive in an increasingly AI-dependent business environment while contributing to the broader goal of safe and beneficial AI development and deployment.
The future of AI security will continue to evolve as new threats emerge and as defensive technologies advance, but the fundamental principles and frameworks outlined in this series provide a solid foundation for building security capabilities that can adapt and evolve with changing circumstances. By implementing comprehensive AI security solutions today, organizations can prepare for tomorrow’s challenges while realizing the transformative potential of artificial intelligence technology.
Your journey to AI security excellence begins with understanding the threats, continues with implementing comprehensive solutions, and evolves through continuous improvement and adaptation. The investment you make in AI security today will determine your organization’s ability to succeed in an AI-powered future while maintaining the security, trust, and confidence that are essential for sustainable business success.
Complete Series Navigation:
– The AI Security Crisis: Why Traditional Cybersecurity Falls Short (Part 1 of Series)
– Understanding AI Software Architecture: Security Implications Across Deployment Models (Part 2 of Series)
– The Four Pillars of AI Security: Building Robust Defense Against Intelligent Attacks (Part 3 of Series)
– Direct Prompt Injection Attacks: How Hackers Manipulate AI Systems Through Clever Commands (Part 4 of Series)
– Indirect Prompt Injection: The Hidden Threat Lurking in Your Data Sources (Part 5 of Series)
– Prompt Leaking Attacks: When AI Systems Reveal Their Secrets (Part 6 of Series)
– AI Model Poisoning and Adversarial Attacks: Corrupting Intelligence at the Source (Part 7 of Series)
– Enterprise AI Governance: Building Comprehensive Risk Management Frameworks (Part 8 of Series)
– Implementing AI Security Solutions: From Strategy to Operational Reality (Part 9 of Series)
– Advanced AI Security Technologies: Cutting-Edge Solutions for Modern Threats (Part 10 of Series)
– The Future of AI Security: Emerging Trends and Next-Generation Threats (Part 11 of Series)
– Building Complete AI Security Solutions: Your Comprehensive Implementation Guide (Part 12 of Series – This Article)
Related Resources:
– Preventing and Mitigating Prompt Injection Attacks: A Practical Guide
– Advanced Security Practices Category
This concludes our comprehensive 12-part series on AI security. For ongoing updates on AI security trends, threats, and solutions, subscribe to our newsletter and follow our advanced security practices content.
Ready to implement comprehensive AI security for your organization? Contact our cybersecurity experts for personalized consultation and implementation guidance.