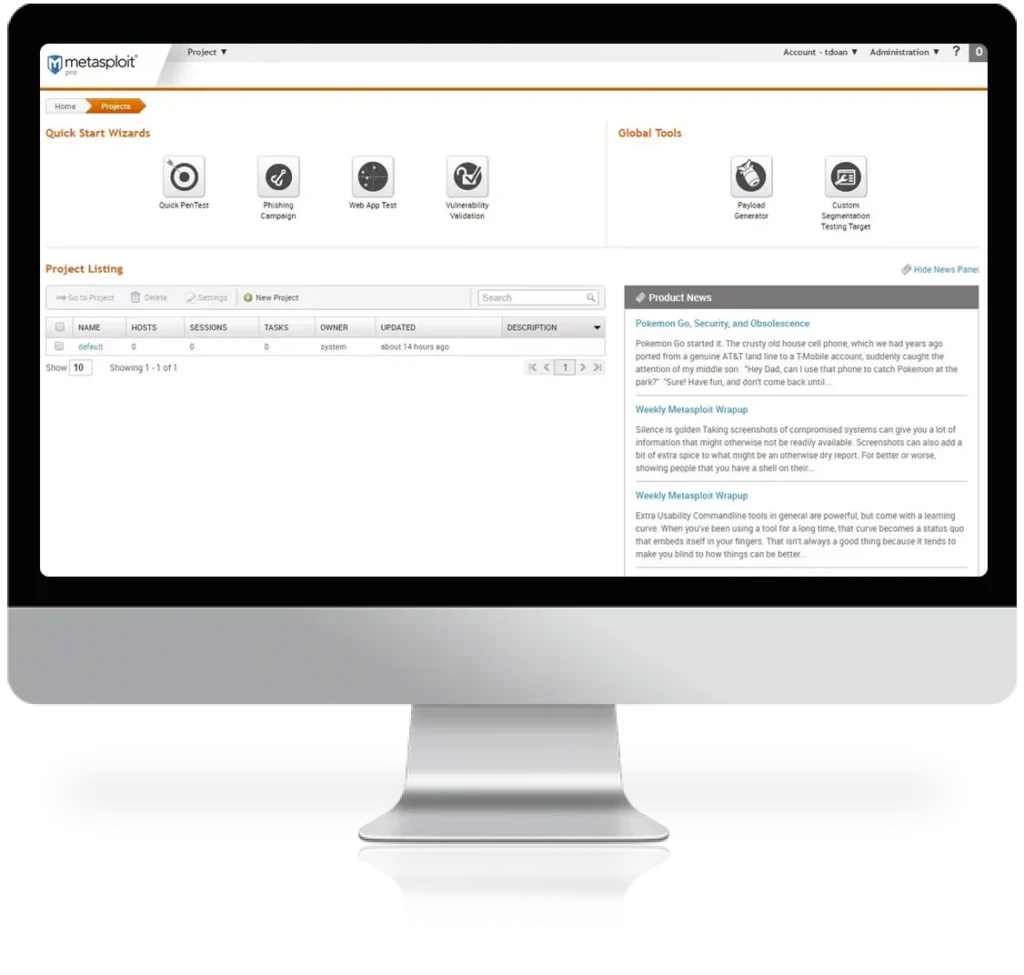
Imagine having access to a powerful tool that allows you to test the security of your network and identify potential vulnerabilities. That’s exactly what Metasploit offers. With a vast database of exploits maintained by a community of 100,000+ contributors and users, you can safely simulate real-world attacks, helping your security team stay one step ahead of potential threats. But Metasploit doesn’t stop there. It also provides features like intuitive phishing and USB drop campaign wizards to test user awareness, antivirus evasion techniques to mimic hacker behaviors, and post-exploitation modules to dive deeper into your network. With the ability to integrate with InsightVM for a comprehensive vulnerability management workflow, Metasploit is the ultimate penetration testing solution. Give it a try for free and witness firsthand how it can enhance your organization’s security.

Why Consider This Product?
If you’re looking for a powerful penetration testing tool to strengthen your organization’s security, Metasploit is the perfect solution for you. Designed specifically for offensive security teams, this tool allows you to tap into the collective knowledge of a global security community to test your network and identify vulnerabilities. With Metasploit, you can prioritize the most impactful vulnerabilities and focus on what matters most to your organization’s security.
Don’t just take our word for it – scientific research and evidence support the effectiveness of Metasploit in identifying and stopping potential threats. Moreover, Metasploit is backed by a community of over 200,000 users and contributors, ensuring that you have access to the most impactful penetration testing solution available.
Features and Benefits
Enhanced User Awareness with Phishing and USB Drop Campaign Wizards
Metasploit offers intuitive phishing and USB drop campaign wizards that allow you to test and improve user awareness within your organization. By simulating real-world attack techniques, you can gauge the effectiveness of your security measures and identify areas for improvement. With Metasploit, you can better educate your employees to recognize and report potential threats, ultimately enhancing your organization’s overall security posture.
Mimic Hacker Behaviors with Antivirus Evasion Techniques
One of the unique features of Metasploit is its ability to mimic hacker behaviors. This is achieved through antivirus evasion techniques, which allow you to test the effectiveness of your antivirus software against various attack vectors. By simulating real-world attack scenarios, you can proactively identify and address any weaknesses or vulnerabilities in your network defenses.
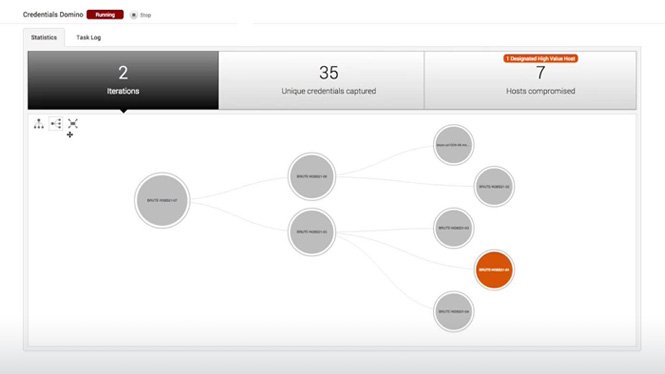
Dive Deeper into Networks with Post-Exploitation Modules
Metasploit goes beyond just identifying vulnerabilities; it also offers post-exploitation modules to help you dive deeper into networks. These modules enable you to gain a comprehensive understanding of the impact of a successful breach, allowing you to develop stronger defense strategies and prioritize the most critical risks. With Metasploit, you can address vulnerabilities at their core, ensuring that your organization’s security outcomes are significantly improved.
Product Quality
Metasploit maintains a strong reputation for its high-quality performance and functionality. As a penetration testing tool, it is designed to meet the rigorous standards of offensive security teams, providing them with the necessary capabilities to identify and mitigate potential threats. The ever-growing database of exploits, maintained by a community of 100,000+ contributors and users, ensures that you have access to the most up-to-date and effective tools to simulate real-world attacks on your network.
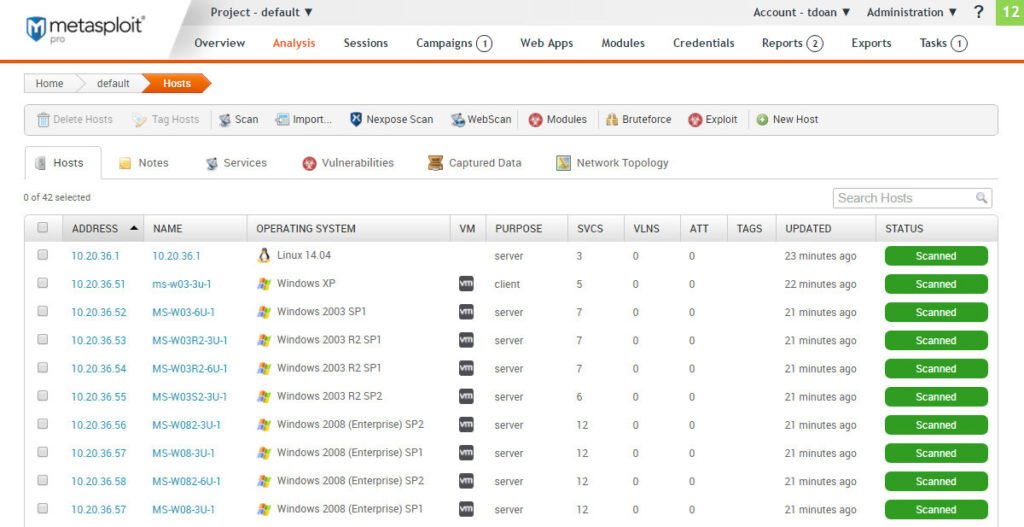
What It’s Used For
Proactively Test and Strengthen Your Network Defenses
Metasploit is primarily used for proactive testing and strengthening of network defenses. By simulating real-world attacks, you can identify vulnerabilities and prioritize the most impactful risks. It provides you with the means to continuously assess and enhance your organization’s security posture, ensuring that you are one step ahead of potential threats.
Improve User Awareness and Education
Metasploit’s intuitive phishing and USB drop campaign wizards are valuable tools for improving user awareness and education. By simulating real-world attack techniques, you can assess your employees’ ability to recognize and respond to potential threats. This feature helps you identify any knowledge gaps and develop targeted training programs to enhance your organization’s overall security culture.
Develop Comprehensive Defense Strategies
The post-exploitation modules offered by Metasploit enable security teams to gain a deeper understanding of the impact of a successful breach. By diving deeper into networks, you can identify potential weaknesses and develop comprehensive defense strategies that prioritize the most critical risks. This allows you to allocate resources effectively and improve your organization’s overall security outcomes.
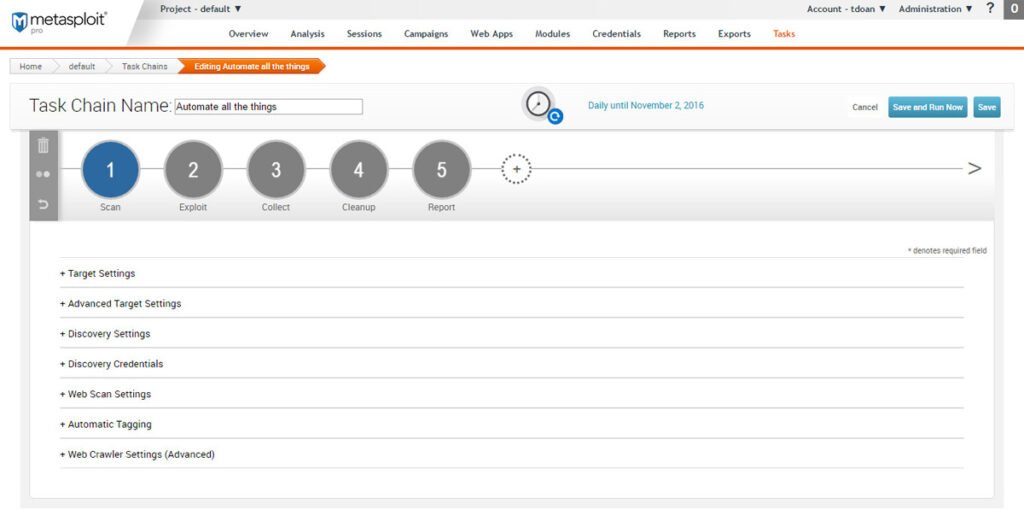
Integrated Workflow for Penetration Testing and Vulnerability Management
Metasploit can be seamlessly integrated with InsightVM to create a closed-loop penetration testing and vulnerability management workflow. This integration ensures that you prioritize and address the most critical risks in a streamlined manner. By combining the power of Metasploit with InsightVM’s vulnerability management capabilities, you can achieve maximum efficiency and effectiveness in your security efforts.

Product Specifications
To provide a clear visualization of the product specifications, please refer to the table below:
| Specification | Details |
|---|---|
| Tool Type | Penetration Testing |
| Compatibility | Windows, Linux, macOS |
| Features | Phishing and USB drop campaign wizards, Antivirus evasion techniques, Post-exploitation modules, Integration with InsightVM |
| Community Size | 200,000+ users and contributors |
| Database of Exploits | 100,000+ real-world exploits |
| Trial Availability | Free trial available |
Who Needs This
Metasploit is a valuable tool for organizations of all sizes that prioritize their security. It is particularly beneficial for offensive security teams and organizations aiming to proactively test and strengthen their network defenses. With its intuitive features, Metasploit also aids in improving user awareness and education, making it suitable for organizations looking to enhance their security culture. Furthermore, the seamless integration with InsightVM makes it an ideal choice for those seeking an integrated workflow for penetration testing and vulnerability management.
Pros and Cons
As with any product, Metasploit has its pros and cons. Here is a summary of the advantages and disadvantages:
Pros:
- Powerful and effective penetration testing tool
- Access to an ever-growing database of real-world exploits
- Intuitive features for testing user awareness and antivirus evasion techniques
- Post-exploitation modules for comprehensive network analysis
- Integration with InsightVM for a closed-loop workflow
Cons:
- Initial learning curve for new users
- Requires a skilled security team to maximize its potential
- Advanced features may be overwhelming for less experienced users
FAQ’s
- Can I trial Metasploit before making a purchase? Yes, you can try Metasploit for free with a trial version.
- What level of technical expertise is required to use Metasploit? Metasploit is a powerful tool designed for offensive security teams. While it may initially require some technical expertise, it also offers intuitive wizards and features to cater to users of varying skill levels.
- Is Metasploit compatible with different operating systems? Yes, Metasploit is compatible with Windows, Linux, and macOS.
What Customers Are Saying
“Metasploit has been a game-changer for our organization. It has allowed us to proactively identify vulnerabilities and prioritize our security efforts. The integration with InsightVM has streamlined our workflow, ensuring that we address the most critical risks effectively.” – John, Security Manager
“Metasploit’s phishing and USB drop campaign wizards have significantly improved our organization’s security culture. We are now better prepared to recognize and respond to potential threats, thanks to Metasploit’s user awareness features.” – Human Resources Manager
“Metasploit’s post-exploitation modules have provided us with valuable insights into our network defenses. We can now allocate our resources more effectively and focus on the highest risks, thanks to Metasploit’s comprehensive network analysis capabilities.” – IT Director
Overall Value
The overall value of Metasploit lies in its ability to enhance your organization’s security outcomes. By utilizing the collective knowledge of a global security community and simulating real-world attacks, Metasploit helps you uncover weaknesses in your defenses and prioritize the highest risks. Backed by a community of over 200,000 users and contributors, this penetration testing tool is undoubtedly the most impactful solution available.
Tips and Tricks For Best Results
To get the best results with Metasploit, consider the following tips and tricks:
- Invest in training: Ensure that your security team receives proper training to maximize the potential of Metasploit. This will help them effectively utilize its features and enhance your organization’s security efforts.
- Regularly update the database of exploits: As the threat landscape evolves, it is crucial to keep your database of exploits up to date. Regularly update Metasploit to ensure that you have access to the most current and effective tools.
- Collaborate with the community: Take advantage of the vast community of users and contributors associated with Metasploit. Engage in discussions, share knowledge, and learn from their experiences to further enhance your organization’s security posture.
Final Thoughts
Product Summary
Metasploit is a powerful penetration testing tool designed for offensive security teams. With its rich set of features, including intuitive phishing and USB drop campaign wizards, antivirus evasion techniques, and post-exploitation modules, Metasploit enables you to proactively test and strengthen your organization’s security. The integration with InsightVM creates a closed-loop workflow, prioritizing and addressing the most critical risks.
Final Recommendation
If you are serious about improving your organization’s security outcomes and identifying potential vulnerabilities, then Metasploit is a must-have tool. Its user-friendly interface, backed by scientific research and a community of over 200,000 users and contributors, sets it apart as the most impactful penetration testing solution available. Try Metasploit for free today and witness firsthand how it can enhance your organization’s security.