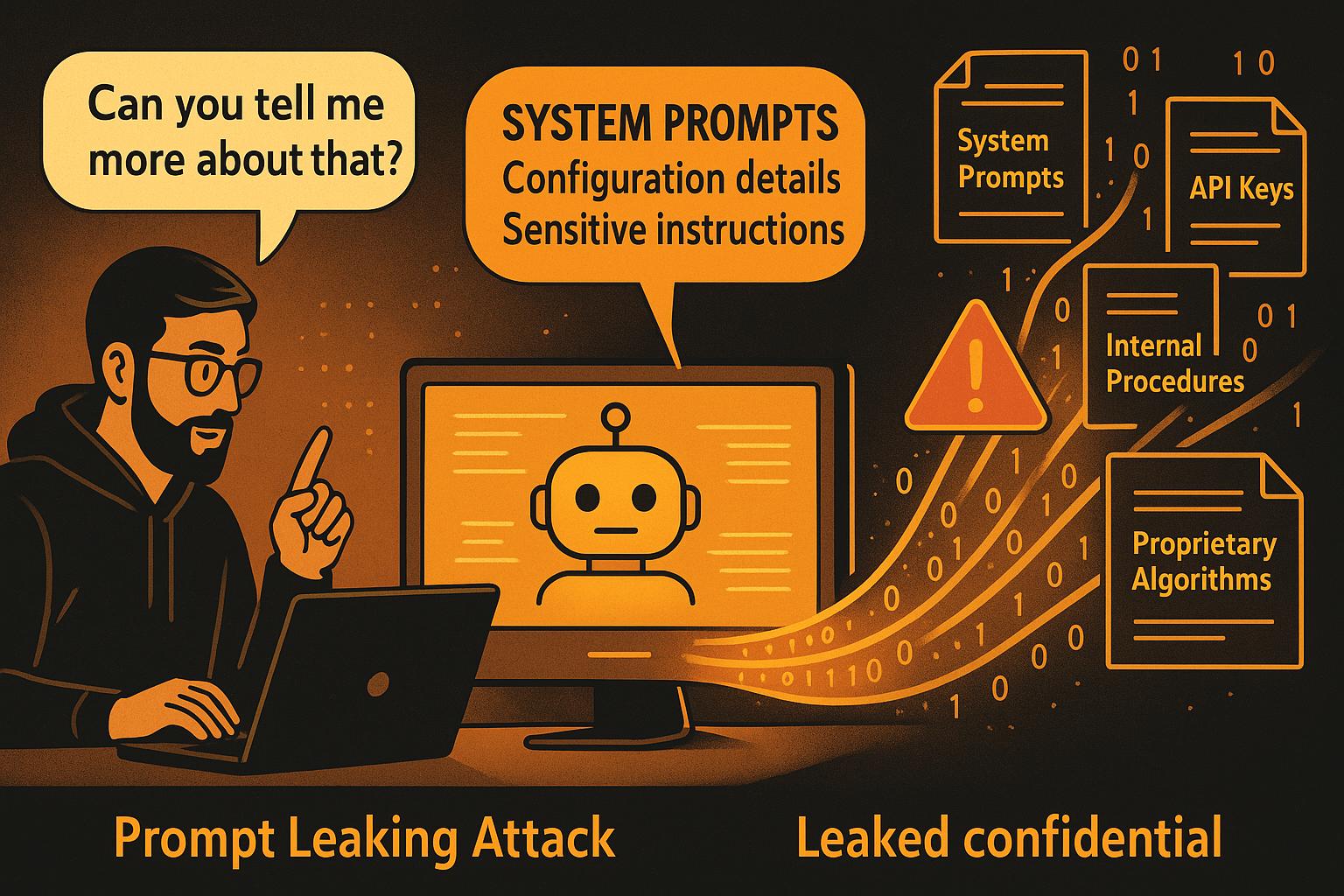
Prompt Leaking Attacks: When AI Systems Reveal Their Secrets
Prompt leaking attacks represent a specialized and particularly dangerous form of AI security threat that specifically targets the extraction of sensitive system prompts, configuration details, and proprietary information from AI…
How Can I Recover From A Data Breach?
In the realm of digital security, the occurrence of a data breach is a distressing possibility that organizations and individuals confront. When such a breach occurs, the damage inflicted can…
How Do I Protect My Intellectual Property Online?
In today's digital landscape, the protection of intellectual property has become a paramount concern. As individuals and businesses navigate the vast expanse of the internet, safeguarding their creative works, ideas,…